

Microsoft Copilot agents are multiplying across your organization. Get the governance to match.
Your data already lives in Microsoft 365. Copilot puts it to work: automating workflows, surfacing insights, and handling tasks so your teams can focus on what matters.
Orchestrate multi-step tasks like document summarization, meeting follow-ups, email triage, and HR requests, all within your existing M365 environment.
Use Copilot agents to draft content, surface insights, and streamline approvals so teams spend less time on repetitive work and more time on what matters.
Let business users build and deploy agents without writing a single line of code, no engineering backlog required
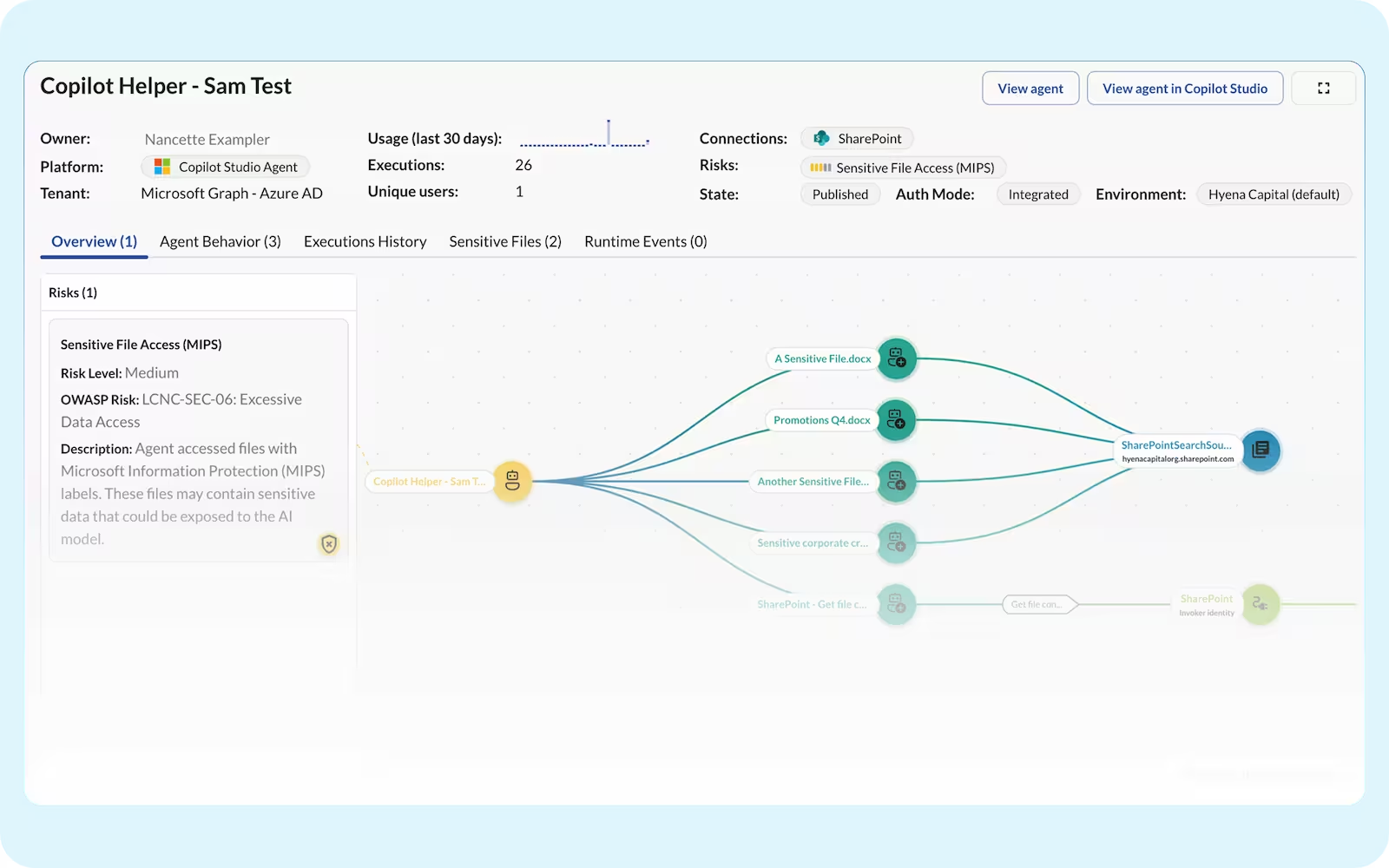
Every Copilot agent inherits user permissions and operates across your M365 environment Without visibility into what they're doing, risky actions and data access go undetected until it's too late.
Copilot inherits user permissions, often retaining excessive or outdated access even after roles change.
Teams spin up agents without central oversight, leaving ownership and permissions untracked.
Attackers or insiders can direct Copilot to pull sensitive information from connected SaaS apps.
A Copilot agent wired to SharePoint, Exchange, or a business-critical app with read/write access can delete files, exfiltrate data, or execute unauthorized transactions with no guardrails to stop it.
Microsoft surfaces your agents but can’t show you every risk, leaving security teams blind to unauthorized tool calls, excessive permissions, and unsanctioned cross-service actions.
No single view of which agents, MCP servers, and models are running across your tenants.
Native logs weren't built to capture risky tool calls and cross-service actions, especially from agents running outside Copilot on platforms like Claude.
Agent permissions are scattered across every app they touch. Without a unified view, you can't know your true exposure until something goes wrong.
Agents act on behalf of users but aren't always bound by the same limits. Without a full identity graph, you won't know when an agent quietly exceeds the access its user was granted.
Map, monitor, and manage your agents with a single governance layer.

.avif)
.avif)
.avif)